Quantum Technologies and the Future of Cryptography: Three Scenarios for 2035
APR 24, 2026 / BY VICTOR KERROS
The opinions, interpretations, and conclusions expressed in this article are solely those of the author(s) and do not necessarily reflect the views of their employers, affiliated institutions, or any organizations with which they are associated. The author(s) bear full responsibility for the content.
By 2035, cryptography will be one of the clearest areas of impact of quantum technologies.
Today’s digital security relies on mathematical problems that are (very) hard for classical computers. Quantum computers challenge this assumption. Shor’s algorithm can break widely used protocols such as RSA cryptosystem and elliptic curve cryptography that secure internet traffic, financial systems, and blockchain-based cryptocurrencies. The full risk is still uncertain as quantum computing remains an early field. More efficient algorithms could emerge, and existing ones could improve further as scientists gain access to more advanced hardware to test their ideas.
This is why governments are investing billions to develop the technology, to avoid falling behind and being exposed to adversaries without a credible response.
Fortunately, in 2024, the U.S. National Institute of Standards and Technology (NIST) approved a first set of post-quantum cryptographic (PQC) protocols1. These are designed to remain secure even in the presence of cryptographically relevant quantum computers (CRQC), meaning machines capable of running Shor’s algorithm at a scale that breaks RSA. At the same time, quantum technologies may (paradoxically) also contribute to security: Quantum Key Distribution (QKD), a protocol that leverages quantum mechanical properties such as entanglement, could offer a way to protect communications against interception and has already demonstrated promising results2. But the transition to a secure post-quantum world won’t be straightforward.
This article examines what the cryptography world could look like in 2035 as quantum technologies move toward practical use. It considers three scenarios:
- Status-quo: quantum computers have not reached a size where they can break current cryptography – but risk remain in this scenario, as we will see,
- Best-case: quantum computers can run Shor’s algorithm at scale (and other scientific use applications), but systems have migrated to PQC so the world is safe, isn’t it?
- Worst-case: quantum computers can run Shor’s algorithm, but migration to PQC is incomplete – this is chaos.
For each scenario, the analysis assesses its likelihood and the economic and societal impact of the technological outcome.
1. Status-quo: quantum computers have not yet reached a size where they can break current cryptography
1.1. This world is unlikely: recent progress suggests CRQC is getting closer
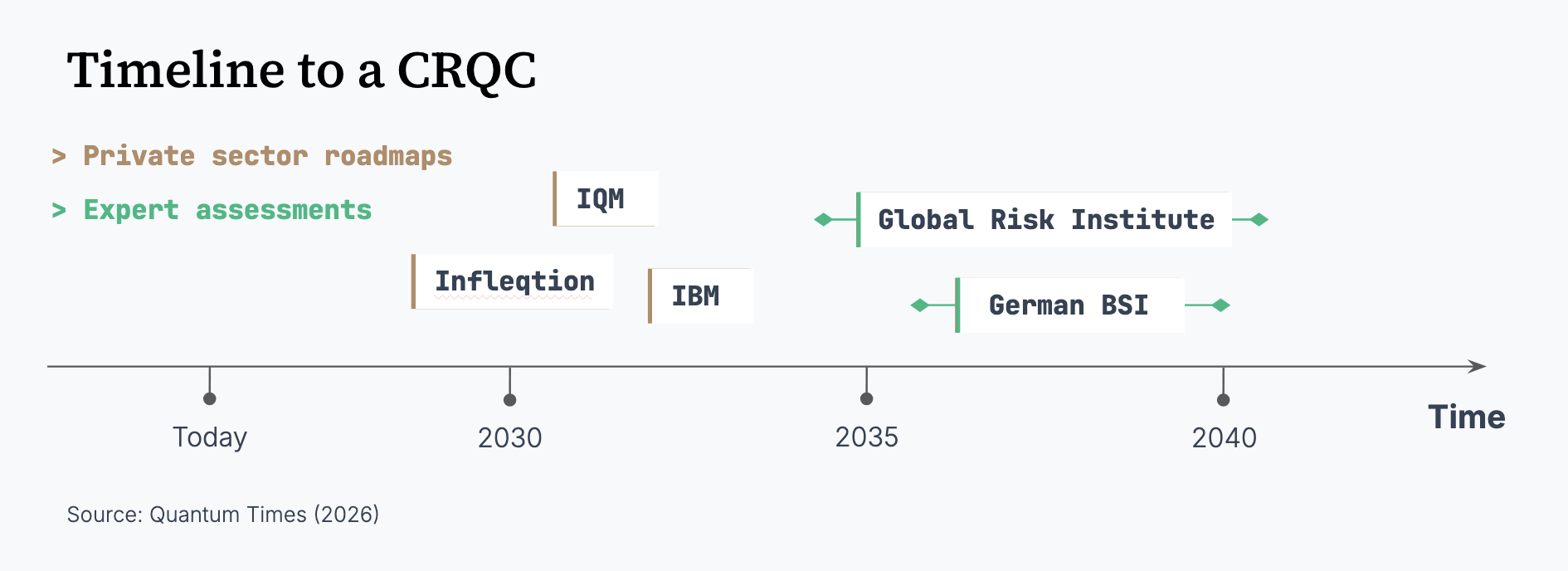
Since the late 2010s, following milestones such as Google Quantum AI’s 2019 “quantum supremacy” demonstration, the debate has shifted from if to when3. Recent expert surveys reflect this shift, with a CRQC by 2035 now within the realm of possibility. The latest report from the Global Risk Institute (published in March 2026) places the 10-year likelihood of a CRQC between 28% and 49%, the highest level recorded to date4. Government risk assessments point in the same direction: the US Department of Homeland Security assumed that a CRQC could be “potentially available” as early as 20305 and the German Federal Office for Information Security (BSI), in its 2025 update on the status of quantum computer development, estimated that a CRQC could emerge within 10-15 years6.
Two factors motivate these updated assessments:
- On the hardware front, recent progress suggests that one of the three key barriers – quality, quantity, speed – to CRQC has fallen: quality7. Google’s 2024 experiment showed that error correction can effectively suppress errors enabling longer quantum computations8, necessary to run Shor’s algorithm (which requires in the order of several trillion reliable quantum computing operations). Many scientists now believe that there is no strong scientific or theoretical obstacle preventing the creation of a CRQC – it’s a matter of engineering to scale. And some vendors anticipate CRQC relevant quantum computers before 20359.
- At the same time, quantum resource estimates for quantum cryptanalysis are shrinking. Five years ago, projections required tens of millions of qubits to break RSA10,11 but more recent estimates suggest sub-million12, and potentially sub-100k with optimized qubit architectures13,14,15. Similar trends apply to elliptic curve cryptography16. Taken together, these developments make the “status-quo” scenario increasingly unlikely as the hardware could meet the software earlier in time.

1.2. Why this world is likely: hardware challenges remain important – but the risk is not going to disappear, it can only get worst
Two barriers to realizing a CRQC remain: scaling and speed.
- Speed determines whether a quantum attack is operationally relevant. A quantum attack that takes decades – because the quantum computer cannot process more than a million operations per second – does not constitute a credible threat. Some qubit modalities, often those leading the scoreboard when it comes to lowering qubit counts, are still slow which makes them irrelevant for most quantum attacks16.
- Scaling still presents “significant outstanding challenges” according to the study “How to Build a Quantum Supercomputer: Scaling from Hundreds to Millions of Qubits” co-led by scientists from the supercomputer developer Hewlett Packard Enterprise (HPE) and the recent Physics Nobel Prize John Martinis17. Key issues include interconnection of quantum computing modules or maintaining fidelity at large scale.
Therefore, hardware remains the main bottleneck today, even while algorithmic progress is compressing the attack resource estimates. Engineering a CRQC-scale system is still orders of magnitudes beyond what has been achieved today.
Also, several factors could still slow down the development of a CRQC. Sustained private funding remain dependent on the economic context and could shrink, especially if commercially viable applications outside cryptography fail to materialize4. In parallel, geopolitical tensions – including export controls18 or closed-source research – could fragment development efforts (so far very international and open) and delay progress19.
But a single breakthrough on the hardware side (e.g. a very performant quantum interconnect technology to make quantum computing efficiently modular) would make CRQC achievable in a matter of few years. Indeed, once the science is solved, the history of computing suggests that scaling follows quickly: today’s supercomputers are 16 orders of magnitude more powerful than the ones from the 1950s (e.g. the ENIAC).
1.3. Societal impact in this scenario can still be significant: risk is more in the Q-transition, not Q-day
In a recent work, researchers at Google chose to limit disclosure of their quantum-enabled cryptanalytic advances, noting that progress has reached a stage where detailed publication of the algorithm could enable misuse in the near future20. Their message is clear: the risk of a CRQC becoming available in the near term will not disappear, it can now only get worse. Indeed, multiple hardware platforms are advancing in parallel, and theoretical objections to the feasibility of a CRQC – such as Gil Kalai’s correlated noise argument, which suggests that errors may be correlated rather than independent, complicating quantum error correction at scale – are increasingly constrained by experimental progress21. As a result, the 2026 Global Risk Institute places the 30-year likelihood of a CRQC above 80%4. It will eventually be built31.
Therefore, migration to PQC cannot wait for certainty. The mere possibility that a CRQC becomes available in the foreseeable future – even if not as early as 2035 – is sufficient to trigger action now.
However, the transition itself introduces new risks. Indeed, migrations could break things more than they fix: increased exposure to downgrade attacks, misconfigurations, and side-channel vulnerabilities16,22,44, even if a CRQC never materializes because scaling and/or speed remain bottlenecks. If PQC transition were to be managed poorly in critical sectors, such as banking or communications, there could be a confidence shock: a sudden loss of trust in the integrity of digital systems, a “cryptographic bank run”. Therefore, the scenario where CRQC is not available does not mean that risk is absent. One could say: the risk is more in the Q-transition, not Q-day44. “Cryptographic agile organization”22, whether governments or companies, will have a decisive edge in maintaining the trust of citizens and customers (and attracting them).

2. CRQCs exist, but migration to PQC has succeeded
2.1. Why this is a likely scenario: migration to PQC is already starting
Since the certification of new PQC protocols by the NIST in 2024, deployment has begun across both public and private systems. For instance, some blockchain systems are already entirely relying on PQC such as Quantum Resistant Ledger, Mochimo, and Abelian, while some others have initiated PQC deployments16. In March 2026, Google released a roadmap targeting 2029 for broad PQC migration23 and showed in a blog post that Android 17 already implements PQC “deep into the platform”24. A few weeks after, Cloudflare has similarly committed to PQC deployment across its network stack within this timeframe and presented that over 65% of human traffic to Cloudflare is already post-quantum encrypted25. Microsoft’s roadmap aims to complete transition of its services and products by 203326. These actors control large portions of global digital infrastructure, making their timelines structurally impactful.
Governments are also structuring this transition and most of them target the 2035 deadline for full migration, though most of them also urge agencies to start the transition of critical systems as soon as possible. For instance, the European Commission has published a Coordinated PQC Transition Roadmap that requires all EU member states to begin deploying post-quantum encryption by 202627. Canada aimed at completion of PQC migration of high priority systems by end of 203128. The US National Security Agency also published a report in 2025 in which it “expects the transition to QR [Quantum Resistant] algorithms for NSS [National Security Systems] to be complete by 2035”29.
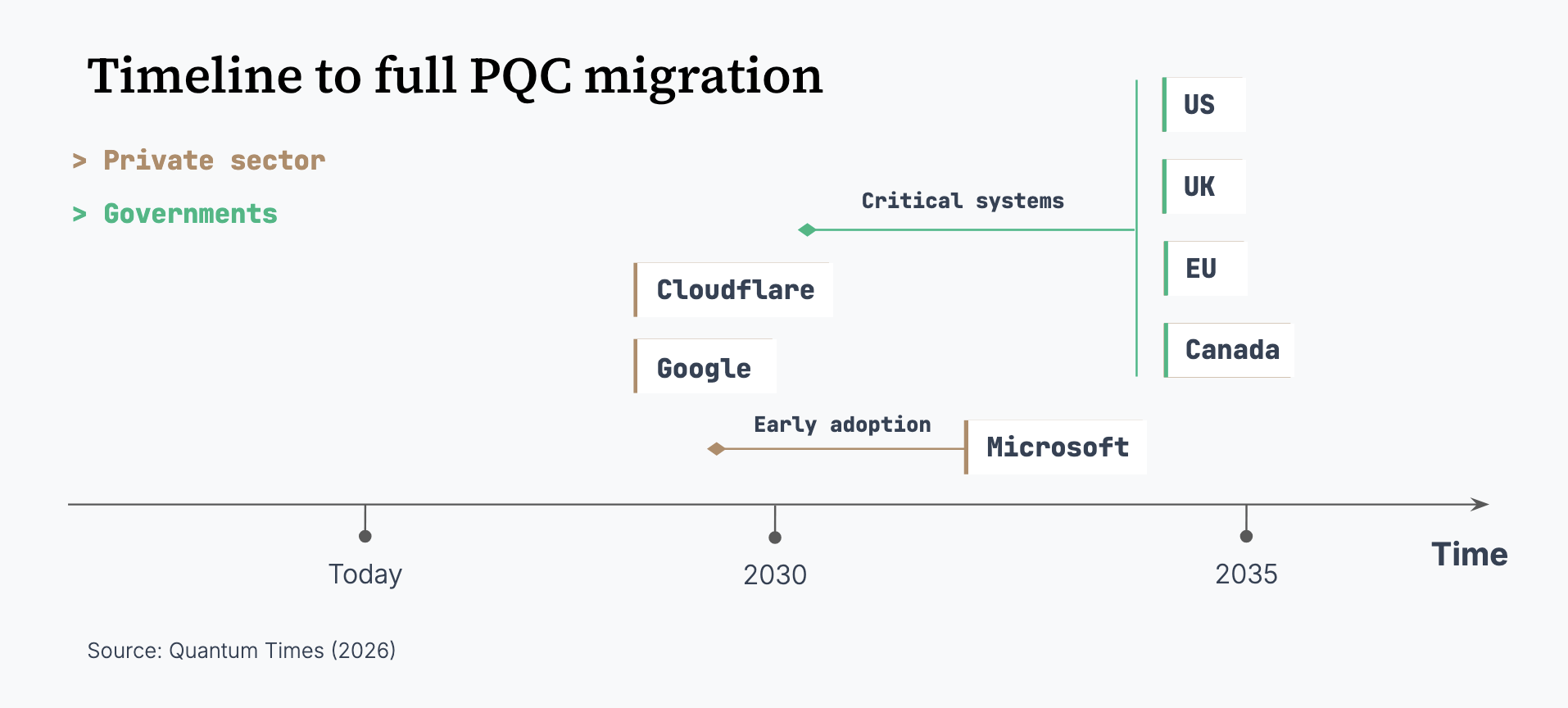
Whilst private companies seem to have shorter timelines to PQC migration, the direction is consistent: PQC migration is underway and accelerating, since most big tech players or governments have published a roadmap update over the past two years and already started implementing it.
Furthermore, in this scenario, the availability of a CRQC would reflect a broader maturation of quantum engineering. This, in turn, makes the emergence of quantum-secured communication infrastructures, particularly those based on QKD, increasingly plausible. The latest large-scale deployment of China’s 10,000-kilometer quantum communication network illustrates that the underlying technologies are already progressing toward real-world implementation2,30.
It is therefore credible to think that the world will be ready for a CRQC by 2035.
2.2. In this scenario, the threat remains even after migration
Even with a successful transition to PQC, the risk does not disappear. The most immediate concern is “Harvest Now, Decrypt Later” (HNDL): adversaries can collect encrypted data today and decrypt it once quantum capabilities mature. This creates a present-day risk tied to the « shelf life » of data (= how many years the data must remain secure for). In a podcast, Justin Thaler (Associate Professor of Computer Science at Georgetown University) warned that « China today is probably hoovering up all encrypted U.S. government communications that they can get« , with the intent to decrypt them once a CRQC becomes available45.
Moreover, instability may continue to emerge even if PQC adoption is successfully managed by enterprises and governments. Indeed, unlike RSA or ECC, which have been scrutinized for decades and are safe against classical computing attacks, PQC schemes are relatively new. As noted in section VII of a recent analysis from Google, undiscovered weaknesses in today’s PQC NIST-standardized schemes remain a credible risk, both from classical and potential future quantum attacks16. This is not hypothetical: researchers at KU Leuven demonstrated that a candidate scheme that made to the fourth round of NIST’s standardization effort could be broken using a single core in a few minutes32. In other words, PQC cannot be considered fully robust until it has undergone years of adversarial testing at scale. For quantum attacks, the authors note that there could be “unexpected breakthroughs” on lattice-based or learning-with-errors-based cryptosystems, so far thought to be post-quantum safe16.
2.3. Economic impact of a successful PQC migration will be significant
A study by BCG estimates that PQC migration could represent 2.5% to 5% of annual IT budgets, based on early deployments and lessons from the Year 2000 problem (noting that preemptive planning could significantly reduce this amount). For instance for telecommunications companies it could reach hundreds of millions of dollars per operator33and the United States Federal Government has estimated total migration costs at $7.1 billion between 2025 and 203534.
Beyond cost, the transition could still affect trust in digital systems as the shift from if to when becomes clearer: even if successful, migration may create new winners, as vulnerabilities or delays trigger loss of confidence and reorder market leadership, with lagging actors losing credibility and potentially collapsing.
Finally, in the case of financial services, even a successful migration could have an impact as PQC integration may significantly reduce transaction throughput31,35,36,44. For instance, a project led by the Bank for International Settlements Innovation Hub with the Banque de France and Deutsche Bundesbank, shows that PQC increases VPN setup times, with “significant consequences for time-demanding use cases” such as instant payments, highlighting a trade-off between security and performance35.
3. CRQCs exist, but migration to PQC is incomplete
3.1. Why migration could fall behind CRQC development
As highlighted by BCG in a recent blog post, cryptographic transitions take about a decade, as seen in past shifts from DES to AES or MD to SHA36. It’s a complex, large-scale project for organizations – it requires full cryptographic inventory, prioritization, and phased rollout, and estimates from experts suggest that up to 120,000 discrete tasks are required for large organizations37. The World Economic Forum Global Future Council on Quantum Computing projected in June 2020 that 20 billion devices will need to be upgraded to PQC over the next two decades and refers to PQC as a “massive effort”38. Ecosystem coordination is another major friction, even for the most critical infrastructure. For instance, Bitcoin lack strong governance and migration could take years in practice16, though the whole migration could theoretically be achieved within months39. Furthermore, as discussed in the first part, the materialization of the quantum threat may trigger FUD (fear, uncertainty, and doubt), leading to rushed PQC deployments with immature standards and new vulnerabilities, ultimately slowing PQC migration.
Finally, cost (as presented in section 2) and talent availability constraints will further slow PQC migration. Large technology firms such as Google or Microsoft can invest heavily in the migration, hire the right experts to achieve their ambitious goals, but this is not true for most organizations. Likely laggards include SMEs, emerging markets, legacy-heavy sectors (e.g. healthcare, old industrial systems), and deeply IoT embedded environments. This could create uneven security across the global digital infrastructure. Whether AI agents may help with the migration is still unclear at this stage, especially because of reliability concerns for critical systems.
3.2. Extensive quantum risks in this scenario
In this scenario, risks concentrate around three main exposure types (see illustration): long-lived data (HNDL), weak PQC implementations, and systems that could not migrate to PQC.
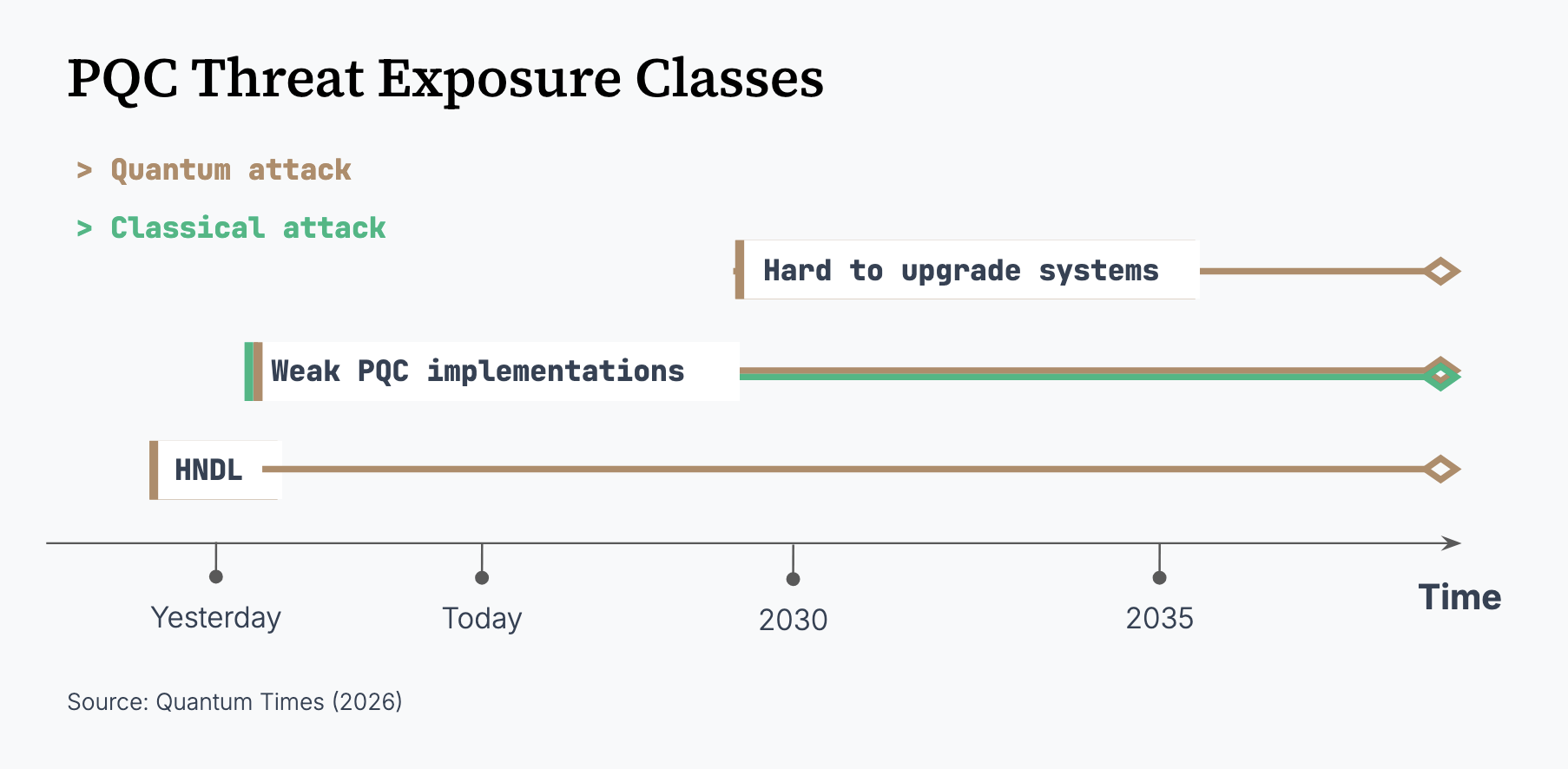
HNDL and weak PQC implementations have already been covered in previous sections. We focus here on systems whose migration lags behind the availability of CRQCs. In this case, the main risk is targeted attacks, not mass disruption. These attacks remain resource-intensive: CRQCs are still expected to cost millions40, if not billions41. As a result, widespread quantum attacks on civilians are unlikely. Instead, high-value systems are the primary targets. A 2023 study by the Hudson Institute estimates that a one-day quantum attack on a major bank connected to the Fedwire system could lead to $2 to $3.3 trillion in indirect losses42. More broadly, uneven migration creates weak links that attackers can exploit.
In parallel, the “trust now, forge later” risk means that attackers with sufficiently powerful quantum computers (the required scale for this is still under study) could forge digital signatures, allowing malicious software or commands to appear legitimate in the future43.
Cryptocurrencies illustrate this vulnerability. If a fast enough CRQC – whether based on superconducting, photonic, or semiconductor technologies – becomes available, networks like Bitcoin could face “on-spend” attacks, where transactions are intercepted and keys are broken before confirmation16. This could lead to loss of funds and/or sharp declines in value, potentially even before such machines exist, as confidence in the cryptosystem erodes.
Finally, continued hardware progress – more specifically orders-of-magnitude improvements in quantum computer speed – could expand the range of viable attacks, including those based on Grover’s algorithm against symmetric encryption (e.g. AES, widely used to secure data storage).
3.3. Arising societal issues
If CRQCs emerge before full migration, the main question is who controls access: these machines are likely to remain concentrated in the hands of a few actors. As noted by BCG, intelligence agencies already show strong interest in these capabilities37. This creates a form of quantum asymmetry: some actors may be able to access or decrypt sensitive information without the targets even knowing they have been compromised. Indeed, when a technology becomes a real security concern, openness tends to fade. As Scott Aaronson pointed out, the Manhattan Project followed that path: research on uranium fission was published, until it wasn’t21. A direct consequence is that beneficial quantum computing applications for society (e.g. in chemistry or materials science) could be restricted, limiting broader societal gains19.
This asymmetry could reshape the geopolitical landscape. Countries that achieve CRQCs first, before others achieve PQC migration may gain strategic advantage, as did the Allies during World War II with the “bombe” or the Colossus used to decipher the German-encrypted messages (e.g. U-boat positions). By 2035, agentic AI systems – already increasingly capable in cryptanalysis – could, once enhanced by CRQCs, continuously discover vulnerabilities, forge credentials, and execute adaptive cyber operations at scale with minimal human oversight. This would shift cyber conflict toward persistent, self-improving attacks that are harder to detect, attribute, and contain, reinforcing first-mover advantages. Therefore, export controls already restrict the diffusion of PQC technologies18, reshaping the geopolitical landscape and making access to secure economies increasingly dependent on strategic alliances with leading quantum tech powers.
A deeper societal issue is the erosion of political privacy in this 2035 scenario. In an increasingly digital and AI-driven world, quantum capabilities could function as a form of Orwellian “telescreen” for authoritarian regimes, enabling large-scale surveillance and making political coordination and dissent more difficult. More insidiously, as described by Michel Foucault’s Panopticon, the mere possibility of surveillance would lead individuals to internalize control and self-regulate, turning this loss of privacy into a structural political conformity.
Conclusion
The future of cryptography depends on the race between quantum advances and our ability to adapt. By 2035, we could see status quo, a controlled transition, or disruption. These are still coexisting possibilities – much like interpretations of the quantum multiverse – until technical, political, and economic choices determine the outcome. Whatever the scenario, risk will not be zero, so action should be timely and neither delayed nor rushed.

Victor Kerros is Chief of Staff at Alice&Bob USA. Previously he was a Data Scientist in the MedTech industry.
References
1National Institute of Standards and Technology, « NIST Releases First 3 Finalized Post-Quantum Encryption Standards », Jul. 2025, (https://www.nist.gov/news-events/news/2024/08/nist-releases-first-3-finalized-post-quantum-encryption-standards) [Accessed: Apr. 23, 2026].
2H.-Z. Chen et al., “Implementation of carrier-grade quantum communication networks over 10000 km,” npj Quantum Inf, vol. 11, no. 1, p. 137, Aug. 2025, doi: 10.1038/s41534-025-01089-8.
3J.-F. Bobier et al., “What Happens When ‘If’ Turns to ‘When’ in Quantum Computing?,” Boston Consulting Group, Jul. 2021.
4M. Mosca, M. Piani, « Quantum Threat Timeline Report 2025 », March 2026, (https://globalriskinstitute.org/publication/quantum-threat-timeline-report-2025b/) [Accessed: Apr. 23, 2026].
5U.S. Department of Homeland Security, « Preparing for Post-Quantum Cryptography », Oct. 2021, (https://www.dhs.gov/sites/default/files/publications/post-quantum_cryptography_infographic_october_2021_508.pdf) [Accessed: Apr. 23, 2026].
6Bundesamt für Sicherheit in der Informationstechnik, « Status of quantum computer development V2.2 », Dec. 2025, (https://www.bsi.bund.de/SharedDocs/Downloads/DE/BSI/Publikationen/Studien/Quantencomputer/Entwicklungstand_QC_V_2_2.pdf?__blob=publicationFile&v=5)[Accessed: Apr. 23, 2026].
7C. Gidney, « Quantum Error Correction goes FOOM », Dec. 2025, (https://algassert.com/post/2503) [Accessed: Apr. 23, 2026]
8Google Research, “Making quantum error correction work,” Google Research Blog, (https://research.google/blog/making-quantum-error-correction-work/) [Accessed: Apr. 23, 2026].
9O. Ezratty, “Understanding Quantum Technologies 2025,” Oct. 2025, doi: 10.48550/arXiv.2111.15352.
10A. G. Fowler, M. Mariantoni, J. M. Martinis, and A. N. Cleland, “Surface codes: Towards practical large-scale quantum computation,” Phys. Rev. A, vol. 86, no. 3, p. 032324, Sep. 2012, doi: 10.1103/PhysRevA.86.032324.
11O. C. Gidney and M. Ekerå, “How to factor 2048 bit RSA integers in 8 hours using 20 million noisy qubits,” Quantum, vol. 5, p. 433, Apr. 2021, doi: 10.22331/q-2021-04-15-433.
12O. Ezratty, “Understanding Quantum Technologies 2025,” Oct. 2025, doi: 10.48550/arXiv.2111.15352.
13D. Ruiz, J. Guillaud, A. Leverrier, M. Mirrahimi, and C. Vuillot, “LDPC-cat codes for low-overhead quantum computing in 2D,” Nat Commun, vol. 16, no. 1, p. 1040, Jan. 2025, doi: 10.1038/s41467-025-56298-8.
14P. Webster et al., “The Pinnacle Architecture: Reducing the cost of breaking RSA-2048 to 100 000 physical qubits using quantum LDPC codes,” Feb. 12, 2026, doi: 10.48550/arXiv.2602.11457.
15M. Cain et al., “Shor’s algorithm is possible with as few as 10,000 reconfigurable atomic qubits,” Mar. 30, 2026, arXiv: arXiv:2603.28627. doi: 10.48550/arXiv.2603.28627.
16R. Babbush et al., “Securing Elliptic Curve Cryptocurrencies against Quantum Vulnerabilities: Resource Estimates and Mitigations,” Apr. 15, 2026, doi: 10.48550/arXiv.2603.28846.
17M. Mohseni et al., “How to Build a Quantum Supercomputer: Scaling from Hundreds to Millions of Qubits,” Mar. 13, 2026, doi: 10.48550/arXiv.2411.10406.
18Y. Tran, « Will Quantum Export Control Secure The Future Or Shatter It? », Quantum Times, Apr. 2026, (https://quantum-times.com/will-quantum-export-control-secure-the-future-or-shatter-it/) [Accessed: Apr. 23, 2026].
19Quantum Times, « Shor’s Algorithm is Quantum’s Pharmakon », Apr. 2026, (https://quantum-times.com/mind-snacks/) [Accessed: Apr. 23, 2026].
20R. Babbush, H. Neven, « Safeguarding cryptocurrency by disclosing quantum vulnerabilities responsibly », Google Research Blog, Mar. 2026, (https://research.google/blog/safeguarding-cryptocurrency-by-disclosing-quantum-vulnerabilities-responsibly/) [Accessed: Apr. 23, 2026].
21S. Aaronson, « The Superposition Guy: Scott Aaronson Interview », The Superposition Guy, Mar. 2026, (https://podcast.yboger.com/2026/03/02/scott-aaronson-professor-of-computer-science-ut-austin/) [Accessed: Apr. 23, 2026].
22A. Amadori et al., « The PQC Migration Handbook », TNO, Dec. 2024, (https://publications.tno.nl/publication/34643386/fXcPVHsX/TNO-2024-pqc-en.pdf) [Accessed: Apr. 23, 2026].
23H. Adkins, « Quantum frontiers may be closer than they appear », Google The Keyword, Mar. 2026, (https://blog.google/innovation-and-ai/technology/safety-security/cryptography-migration-timeline/) [Accessed: Apr. 23, 2026].
24E. Lynch, D. Elliott, « Security for the Quantum Era: Implementing Post-Quantum Cryptography in Android « , Mar. 2026, (https://security.googleblog.com/2026/03/post-quantum-cryptography-in-android.html) [Accessed: Apr. 23, 2026].
25B. Westerbaan, « Cloudflare targets 2029 for full post-quantum security », Apr. 2026, (https://blog.cloudflare.com/post-quantum-roadmap/) [Accessed: Apr. 23, 2026].
26M. Russinovich, M. Braverman-Blumenstyk, « Quantum-safe security: Progress towards next-generation cryptography », Aug. 2025, (https://www.microsoft.com/en-us/security/blog/2025/08/20/quantum-safe-security-progress-towards-next-generation-cryptography/) [Accessed: Apr. 23, 2026].
27European Commission, « A Coordinated Implementation Roadmap for the Transition to Post-Quantum Cryptography », Jun. 2025, (https://digital-strategy.ec.europa.eu/en/library/coordinated-implementation-roadmap-transition-post-quantum-cryptography) [Accessed: Apr. 23, 2026].
28Canadian Centre for Cyber Security, « Roadmap for the migration to post-quantum cryptography for the Government of Canada », Jun. 2025, (https://www.cyber.gc.ca/en/guidance/roadmap-migration-post-quantum-cryptography-government-canada-itsm40001) [Accessed: Apr. 23, 2026].
29National Security Agency | Cybersecurity Advisory, « Announcing the Commercial National Security Algorithm Suite 2.0 », Sep. 2022, (https://media.defense.gov/2025/May/30/2003728741/-1/-1/0/CSA_CNSA_2.0_ALGORITHMS.PDF) [Accessed: Apr. 23, 2026].
30M. Ivezic, « China’s Quantum Networking and QKD — World’s Most Ambitious Quantum Communication Program », Apr. 2026, (https://postquantum.com/china-quantum-ambition/china-quantum-networking-qkd/) [Accessed: Apr. 23, 2026].
31S. Aaronson et al., « Quantum Computing & Blockchain », coinbase Position Paper, Apr. 21, 2026.
32W. Castryck, T. Decru, « An efficient key recovery attack on SIDH », 2022, (https://eprint.iacr.org/2022/975.pdf) [Accessed: Apr. 23, 2026].
33M. Ivezic, « Quantum-Readiness / PQC Full Program Description (Telecom Example) », Sep. 2026, (https://postquantum.com/post-quantum/quantum-readiness-telco/#phase-1-discovery-asset-inventory-and-cryptographic-inventory) [Accessed: Apr. 23, 2026].
34M. Swayne, « White House Report: U.S. Federal Agencies Brace for $7.1 Billion Post-Quantum Cryptography Migration », May 2025, (https://thequantuminsider.com/2024/08/12/white-house-report-u-s-federal-agencies-brace-for-7-1-billion-post-quantum-cryptography-migration/) [Accessed: Apr. 23, 2026].
35R. Auer et al., « Quantum computing and the financial system: opportunities and risks », Oct. 2024, (https://www.bis.org/publ/bppdf/bispap149.pdf) [Accessed: Apr. 23, 2026].
36M. Ur Rehman, « How Quantum Computing Affects Cryptography », Apr. 2026, (https://thequantuminsider.com/2026/04/06/how-quantum-computing-affects-cryptography/) [Accessed: Apr. 23, 2026].
37J.-F. Bobier et al., « How Quantum Computing Will Upend Cybersecurity », Oct. 2025, (https://www.bcg.com/publications/2025/how-quantum-computing-will-upend-cybersecurity) [Accessed: Apr. 23, 2026].
38M. Ivezic, « 120,000 Tasks: Why Post‑Quantum (PQC) Migration Is Enormous », Feb. 2026, (https://postquantum.com/post-quantum/quantum-security-pqc-program-plan/) [Accessed: Apr. 23, 2026].
39Global Future Council on Quantum Computing, « Frequently Asked Questions », World Economic Forum, Jun. 2020, (https://www3.weforum.org/docs/WEF_Global_Future_Council_on_Quantum_Computing.pdf) [Accessed: Apr. 23, 2026].
40J. J. Pont, J. J. Kearney, J. Moyler, and C. A. Perez-Delgado, “Downtime Required for Bitcoin Quantum-Safety,” Oct. 22, 2024, doi: 10.48550/arXiv.2410.16965.
41M. Gould and K. Prebble, “An Economic Analysis of Quantum Computing”, Apr. 2025, (https://docsend.com/view/iyxs3jkteiukwreu) [Accessed: Apr. 23, 2026].
42A. W. Butler, A. Herman, « Prosperity at Risk: The Quantum Computer Threat to the US Financial System », 2023, (https://s3.amazonaws.com/media.hudson.org/04.03.2023+_Butler_Prosperity_at_Risk_Quantum_Report.pdf) [Accessed: Apr. 23, 2026].
43M. Ivezic, « Trust Now, Forge Later (TNFL) – The Overlooked Quantum Threat », Oct. 2025, (https://postquantum.com/post-quantum/trust-now-forge-later/) [Accessed: Apr. 23, 2026].
44J. Thaler, » Quantum computing and blockchains: Matching urgency to actual threats « , Dec. 2025, a16zcrypto blog, (https://a16zcrypto.com/posts/article/quantum-computing-misconceptions-realities-blockchains-planning-migrations/) [Accessed: Apr. 23, 2026].
45J. Thaler, « Quantum computing: What, when, where, how », May 2025, a16z crypto show (https://a16zcrypto.com/posts/podcast/quantum-computing-what-when-where-how-fact-vs-fiction/) [Accessed: Apr. 23, 2026].